Private and Public Keys
Overview
Public-key cryptography (also known as asymmetric cryptography) is crucial to blockchain technology and secure networking protocols because it ensures security, integrity, authenticity, and trustless interaction. This type of cryptography is based on a user's private key, which is essentially a randomly generated number kept secret and used to decrypt messages or sign transactions, and a corresponding public key, which is derived from the private key and used to encrypt messages or verify signatures. The security of public-key cryptography relies on the computational infeasibility of deriving the private key from the public key. Traditional public-key cryptography, based on integer factorization and discrete logarithm problems, suffers from the need for very large key sizes and slow performance. Elliptic Curve Cryptography (ECC) addresses these issues by providing the same level of security with much shorter keys and improved efficiency.
Elliptic curve
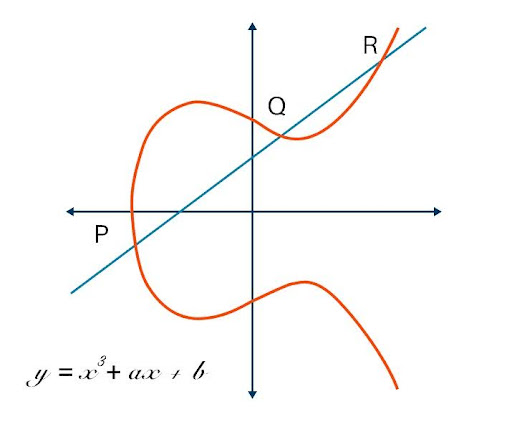
ECC is based on an elliptic curve, a special type of smooth, symmetrical curve defined by an equation involving two variables. The main feature of an elliptic curve that makes it particularly interesting for cryptography is that scalar multiplication is not directly defined as usual multiplication; instead, a point P is multiplied by repeatedly adding P to itself. Such definition of multiplication makes it computationally infeasible to determine the scalar k given the point kP, provided that the set of possible values for k is sufficiently large. An elliptic curve can be defined with an algebraic equation of the following form:
The elegance and efficiency of computation of elliptic curves make them the basis of modern cryptography, balancing security with efficiency in applications like blockchain technology and digital signatures. Addition, the fundamental operation on an elliptic curve, is defined as follows. The sum of points P and Q is the reflection over the x-axis of the third point R where the line through P and Q intersects the elliptic curve. In the case where P = Q, the addition is called doubling. Its result is obtained by drawing the tangent at P, finding its other intersection R with the curve, and reflecting R over the x-axis to get 2P.
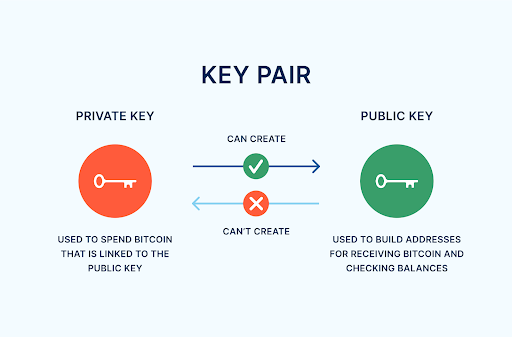
In elliptic curve-based public-key cryptography, a private key is a randomly generated number k, chosen between 0 and 2ⁿ, where n represents the desired security level in bits. For example, if a security level of n = 256 bits is required, the private key k is a 256-bit randomly generated integer, typically expressed as a 64-digit hexadecimal number. This results in an unimaginably large number of possible values, which underpins the cryptographic strength of the system. The corresponding public key is derived from the private key through scalar multiplication: the private key k is multiplied by a predefined generator point G on the elliptic curve. This generator point acts as the identity element for scalar multiplication, meaning that any point on the elliptic curve can be reached by multiplying G by a suitable scalar. This provides a foundation for secure digital transactions because the wallet will utilize the private key to generate a signature for every transaction made that attests to authenticity and integrity of the transaction without exposing the private key.
Private and Public Keys in Bitcoin blockchain
A private key is, in essence, a randomly generated number, and it is usually generated using a secure random number generator. This number is the foundation of Bitcoin's cryptography. The public key associated with a private key is derived by multiplying the private key by a specific generator point on the elliptic curve. The result is another point on the curve, which serves as the public key. The private and public keys are used in the Elliptic Curve Digital Signature Algorithm (ECDSA), based on the secp256k1 curve utilized by Bitcoin, to securely sign and verify transactions.
To create a Bitcoin address from a public key, a series of hashing operations is performed. First, the public key is hashed using the SHA-256 algorithm, resulting in a 256-bit hash. This hash is then passed through the RIPEMD-160 algorithm, reducing it to a 160-bit hash known as the public key hash. Next, a version byte (0x00) is prepended to the public key hash to indicate the Bitcoin network. The SHA-256 algorithm is then applied twice to this new data to produce a checksum, which consists of the first four bytes of the resulting hash. Finally, the combined data (version byte + public key hash + checksum) is encoded using Base58Check. This encoding makes the address human-readable and alphanumeric, resulting in the standard Bitcoin address used for transactions.
Private keys, as the secret ingredient for spending and accessing Bitcoins, should be stored securely. They can be expressed in different formats depending on the intended purpose:
-
Hexadecimal, A 64-character hexadecimal string of the 256-bit number in base-16 form.
-
Base58 Wallet Import Format (WIF), an encoded and concise version of the private key, commonly employed for importing into wallets, including also a checksum for detecting errors.
-
BIP-38 Encrypted Private Keys, a secure method where the private key, which is generally in Base58 WIF format, is encrypted with the AES-256 block cipher.
-
BIP-39 Mnemonic Seed Phrases, A human-readable set of words that can deterministically generate private keys, used for easier backup and recovery.
BIP-38 provides an option for encrypting a private key using a passphrase supplied by the user. The encryption process in BIP-38 uses AES-256 in CBC (Cipher Block Chaining) mode to provide strong protection against unauthorized access. When a user supplies a passphrase, the private key is encrypted using AES-256, and the same passphrase is required to decrypt and use the key in the future. This adds an additional layer of security and makes BIP-38 particularly well-suited for long-term storage solutions such as paper wallets or hardware wallets.
The BIP-38 protocol provides a secure method for private key storage and management in Bitcoin software by enabling passphrase-protected keys. It directly supports the creation of secure paper wallets and facilitates trustless key derivation, addressing key user requirements. The following user stories illustrate practical scenarios where BIP-38's encryption capabilities enhance security and improve usability in Bitcoin transactions.
-
User story: I am a user of Bitcoin and utilize paper wallets. I would like to be able to add encryption, in order for my Bitcoin paper storage to be two factor: something I have in addition to something I know.
-
User story: As a Bitcoin user, I want to send a private key to another person or organization in order to transfer control of funds, without risking that the key is intercepted during transmission, so that the recipient can securely access the funds and unauthorized parties cannot steal them. I would like to give an encrypted private key, and then subsequently provide the password through another method of communication (e.g. phone call or text message).
-
User story: As a user of physical bitcoins, I want a third party to be able to generate password-protected Bitcoin private keys for me without knowing the password, so that I can securely benefit from the physical bitcoin while keeping the private key secret from the issuer. Additionally, I want to choose a password with a minimum length and specific format that is easy for me to remember or record on the physical bitcoin, without increasing the risk of password cracking or theft by the manufacturer.
-
User story: (EC-multiplied keys) As a paper wallet user, I would like to be able to produce many Bitcoin addresses secured by the same password, but with a high level of security (very costly script parameters), without incurring the script slowdown on each address I produce.
Safe storage of the private key is most critical since its compromise translates to loss of funds associated with it, while its loss without backup renders the bitcoins untraceable. Some of the best practices include offline storage (cold wallets), splitting of keys to multiple locations, or seed mnemonic phrases (as per BIP-39) for simple backup. BIP-39 is a standard for generating and recovering cryptographic wallets using a 12 to 24 word sequence, a mnemonic phrase (or seed phrase). The words are used to derive a deterministic key that allows secure storage and recovery of private keys for cryptocurrencies such as Bitcoin.
Key features of BIP-39:
-
Mnemonic phrase: Composed of 12, 15, 18, 21, or 24 words from a standard dictionary of 2048 words (defined in BIP-39).
-
Security: The phrase is an easily memorizable way to back up complex cryptographic keys.
-
Recovery: If you lose your wallet, the phrase allows you to recover all the associated keys and addresses.
-
Compatibility: BIP-39 is implemented by the majority of modern crypto wallets.
-
Process: The sentence is generated from a source of random entropy and then utilized to create a master key.
Summary
Elliptic curves are applied significantly in cryptography, particularly in blockchain technology and Bitcoin, as they can provide high security using shorter keys compared to traditional public-key algorithms, based on integer factorization and discrete logarithm problems. The mathematical properties of elliptic curves render cryptographic operations secure and efficient. A typical feature of elliptic curve is that it is hard to derive the private key from the public key, which is critical for security purposes. The private key, a randomly generated number, is used to sign transactions, while the public key, obtained using the Elliptic Curve scalar multiplication, allows one to verify or encrypt without exposing the private key. However, the most significant issue for the users is securely storing the private key, which can be stored in wallets such as hardware, software, or paper wallets. Compromise or loss of the private key can lead to stolen or inaccessible funds. Specifications such as BIP-39 and BIP-38 mitigate this by providing mnemonic phrases for simple recovery and encrypted storage of the private key, respectively, but users need to embrace best practices such as offline storage or secure backup to secure against vulnerabilities.